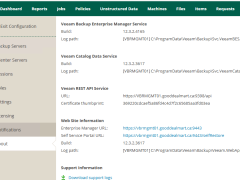
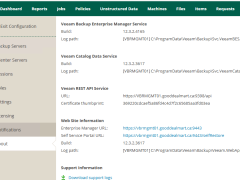
How to Upgrade Veeam Backup Enterprise Manager to v12.3.2.4165
Veeam released the Backup & Replication v12.3.2.4165 on October 14, 2025.
Veeam released the Backup & Replication v12.3.2.4165 on October 14, 2025.
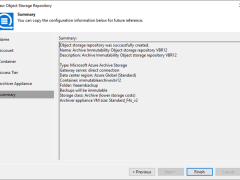
This section explains adding Microsoft Azure Archive Storage as an immutability archive backup repository to the backup infrastructure. This repository can only be used as an archive extension of the scaled-out backup repository.
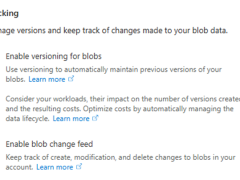
Veeam Backup & Replication allows you to prevent data deletion from the archive extent by making it temporarily immutable. It is done to improve security: immutability safeguards your data against loss due to attacks, malware activity, or other malicious actions.
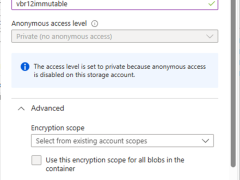
There are some immutability limits in the Azure Blob Storage.
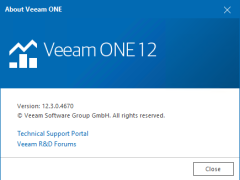
The release version of Veeam ONE 12.3 is available on December 3rd, 2024.
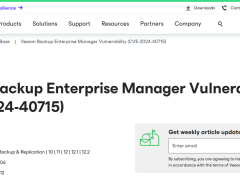
Veeam released the hotfix for the vulnerability in Veeam Backup Enterprise Manager, allowing attackers to bypass the authentication while performing a Man-in-the-Middle (MITM) attack.

The release version of Veeam ONE 12.2 is available on August 28th, 2024.
The vulnerabilities documented in these sections were fixed starting in the 12.2 build.

The release version of Veeam ONE 12.2 is available on August 28th, 2024. You can download it at:
https://www.veeam.com/products/veeam-data-platform/monitoring-analytics.html
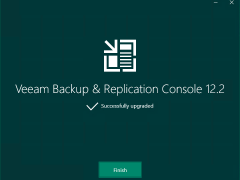
To gain remote access to Veeam Backup & Replication v12.2.0.334, you must first upgrade the Veeam Backup & Replication console to v12.2.0.344 on a dedicated machine.
To gain remote access to Veeam Backup & Replication v12.1.2.172, you must first upgrade the Veeam Backup & Replication console to v12.12.172 on a dedicated machine.
Veeam released Backup & Replication v12.2.0.334 on August 28, 2024.
Veeam Backup & Replication 12.2 is the newer build of version 12, and the major new features and enhancements were added in Veeam Backup & Replication v12.2.

Veeam released Backup & Replication v12.2.0.334 on August 28, 2024.
Veeam released the Backup & Replication v12.1.2.172 on May 21, 2024.
The vulnerabilities documented in these sections were fixed starting in the 12.1.2.172 build.
Veeam Backup Enterprise Manager (VBEM)
CVE-2024-29849 | Severity: Critical (9.8)
This vulnerability in VBEM allows an unauthenticated attacker to log in to the VBEM web interface as any user.
CVE-2024-29850 | Severity: High (8.8)
This Vulnerability in VBEM allows account takeover via NTLM relay.
CVE-2024-29851 | Severity: High (7.2)
This vulnerability in VBEM allows a high-privileged user to steal the NTLM hash of the VBEM service account if that service account is anything other than the default Local System account.
CVE-2024-29852 | Severity: Low (2.7)
This vulnerability in VBEM allows high-privileged users to read backup session logs.

Veeam released the Backup & Replication v12.1.2.172 on May 21, 2024.
The vulnerabilities documented in these sections were fixed starting in the 12.1.2.172 build.
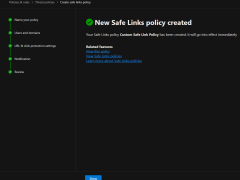
Safe Links is a feature in Microsoft Defender for Office 365 (formerly known as Office 365 Advanced Threat Protection or ATP) that helps protect your organization from malicious hyperlinks in email messages. When an email contains a hyperlink, Safe Links checks the URL against a list of known malicious links. If the link is safe, the user can access the website normally. However, if the link is malicious, Safe Links blocks access to the website and alerts the user and administrators.
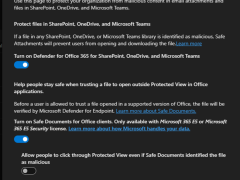
In Microsoft Defender for Office 365, Safe Attachments is a feature that helps protect your organization from malicious email attachments. It automatically scans email attachments for potential threats, such as malware or viruses, before delivering them to recipients’ mailboxes.
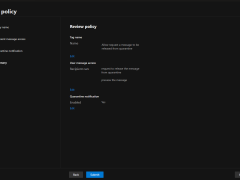
Creating a custom quarantine policy in Microsoft Defender for Office 365 involves configuring advanced threat protection settings to protect your organization’s email environment.
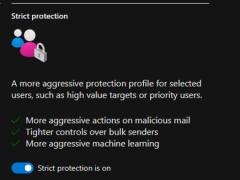
Strict preset security policies typically refer to predefined rules and guidelines designed to enhance security measures within an organization or system. These policies safeguard sensitive data, prevent unauthorized access, and mitigate potential security threats.
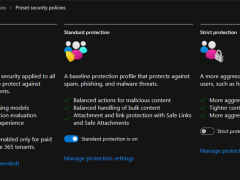
Microsoft Defender for Office 365 provides preset security policies to help organizations protect their Office 365 environment from various threats. These preset policies are designed to offer baseline protection and can be customized according to the organization’s specific requirements.